IED Sensitive Site Exploitation
(SSE) Training
CVE Service Disabled Veteran Owned Small Business
UNIQUE ENTITY ID NB2RPSSAB614
DUNS 032583797 CAGE 6VW15
IED Sensitive Site Exploitation Training gives the attendee thorough understanding of IED's in hostile SSE environments. If you're conducting SSE Operations and have the chance to encounter IED's, this is the training for you!
OBJECTIVE - Sensitive Site Exploitation in an IED Environment
Our Customers Include: SFG, DEA, SWAT
To provide military operators and LEO's, with the necessary skills, techniques, tactics and procedures (TTP’s) needed to optimize their survivability in the IED-laden environment. This will be accomplished through exposure to various IED Narco specific “Booby Trap” scenarios that will provide the attendees with realistic training with increasing levels of difficulty and complexity.
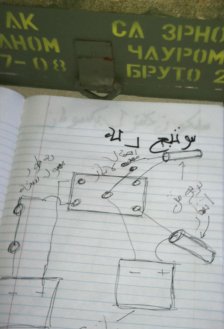
Identification of IED’s to include RC-IED, Booby-Trapped Ordnance, Booby-Trapped Narcotics Labs.
Sensitive Site Exploitation and Evidence collection in a booby-trapped environment.
Identification of heroin and home made explosive precursors.
Safe Separation Distances from known IED's and Weapon Caches.
C-IED/RC-IED Exposure during Convoy and Self-Drive.
Prevent Being Funneled into an IED Zone.
Normally a 4 day course, this training can be abbreviated into time allowed on one day! It's fast paced but we understand the realities of training schedules.
ProceduresDay 1: All personnel will receive a 180 page attendees guide for reference and have the opportunity to have hands-on training, identification of different kinds of IED’s, how the specific IED’s are placed and where. This gives the attendees the key ID features for locating and avoiding IED Kill Zones during convoys, patrols and SSE.
Attendees will be briefed on booby trapped ordnance and safe separation distances from know ordnance.
EOD capabilities will be covered in the event the attendees will have access to EOD assets in country.
Attendees will then walk through a booby trapped drug lab for familiarization to key indicators of explosive manufacturing, IED components and booby trap tactics to enhance their SSE capabilities.
Day 2: Attendees will be forced to pick up the pace with all events being timed based on instructor direction. The attendees will identify common precursors used for the manufacture of heroin and explosives, safe handling, working in a booby trapped environment. Attendees may finish one scenario and move on to the next, ie lab to SSE based on timelines available. Time will be afforded to SGC Group Instructors to reset IED’s and vary scenarios according to the Agents’ abilities.
After Action Reports will take place after each event to clarify points and answer questions and will be driven by the attendees.
Day 3: Attendees will now be exposed to various IED scenarios during convoy operations to and from SSE Investigation Scenarios. Attendees will be exposed to booby trapped narcotics labs, lab equipment and evidence as well as hostile/non-hostile witnesses on objectives. Teams will be expected to collect evidence and tactical interview witnesses in a booby-trapped environment.
Attendees will be forced to finish on time and move on to the next scenario.
Day 4: During the final day of scenarios, teams will be exposed to a full range of IED’s, Kill Zones, booby trapped ordnance, buildings and evidence, friendly and hostile witnesses, hostile forces throughout the infil, investigation and exfil from labs and SSE’s.
Final questions and answers, best practices and lessons learned will be covered to ensure all attendees are prepared for deployment.